Awesome
LDAP Relay Scan
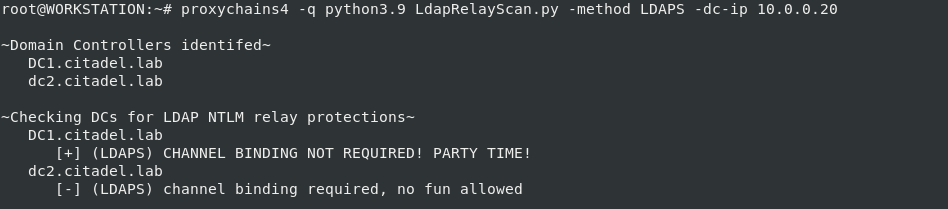
A tool to check Domain Controllers for LDAP server protections regarding the relay of NTLM authentication. If you're interested in the specifics of the error-based enumeration, see below. For details regarding what can be done when you identify a lack of LDAP protections, see the references section.
Summary
There are a couple server-side protections when attempting to relay NTLM authentication LDAP on Domain Controllers. The LDAP protections this tools attempts to enumerate include:
- LDAPS - channel binding
- LDAP - server signing requirements
The enforcement of channel binding for LDAP over SSL/TLS can be determined from an unauthenticated perspective. This is because the error associated with an LDAP client lacking the ability to conduct channel binding properly will occur before credentials are validated during the LDAP bind process.
However, to determine if the server-side protection of standard LDAP is enforced (server signing integrity requirements) the clients credential's must first be validated during the LDAP bind. The potential error identifying the enforcement of this protection is identified from an authenticated perspective.
TL;DR - LDAPS can be checked unauthenticated, but checking LDAP requires authentication.
Installation
It is recommended to use either Docker or a Python virtual environment when running this project.
Docker
- Ensure docker is installed on your machine
- Clone the repository and change directory
git clone https://github.com/zyn3rgy/LdapRelayScan.git && cd LdapRelayScan
- Build the Docker container
docker build -f docker/Dockerfile -t ldaprelayscan .
- [optionally] Ensure the script executes properly
docker run ldaprelayscan -h
Python Virtual Environment
- Ensure python virtualenv is installed on your machine
- Clone the repository and change directory
git clone https://github.com/zyn3rgy/LdapRelayScan.git && cd LdapRelayScan
- Create a Python virtual environment for the project
virtualenv env
- Activate the Python virtual environment
source venv/bin/activate
- Install exact requirement version dependencies
python3 -m pip install -r requirements_exact.txt
- [optionally] Ensure the script executes properly
python3 LdapRelayScan.py -h
Usage
NOTE: DNS needs to resolve properly. If you are routing through SOCKS or running on a non-domain-joined host, ensure this is working.
The tool has two methods, LDAPS (the default), and BOTH. LDAPS only requires a domain controller IP address, because this check can be preformed unauthenticated. The BOTH method will require a username and password or NT hash. The Active Directory domain is not required, it will be determine via anonymous LDAP bind.
arguments:
-h, --help show this help message and exit
-method method LDAPS or BOTH - LDAPS checks for channel binding, BOTH checks for LDAP signing and LDAP channel binding [authentication required]
-dc-ip DC_IP DNS Nameserver on network. Any DC's IPv4 address should work.
-u username Domain username value.
-timeout timeout The timeout for MSLDAP client connection.
-p password Domain username value.
-nthash nthash NT hash of password
Examples
Basic / Virtual Environment Usage Examples
python3 LdapRelayScan.py -method LDAPS -dc-ip 10.0.0.20
python3 LdapRelayScan.py -method BOTH -dc-ip 10.0.0.20 -u domainuser1
python3 LdapRelayScan.py -method BOTH -dc-ip 10.0.0.20 -u domainuser1 -p badpassword2
python3 LdapRelayScan.py -method BOTH -dc-ip 10.0.0.20 -u domainuser1 -nthash e6ee750a1feb2c7ee50d46819a6e4d25
Docker Usage Examples
NOTE: The ability to use SOCKS is passed in using a
PROXY_CONFIGenvironment variable. If SOCKS is required, the--network=hostflag will also need to be used to correctly route traffic. See examples below.
docker run ldaprelayscan -h
docker run ldaprelayscan -dc-ip 10.0.0.20
docker run ldaprelayscan -dc-ip 10.0.0.20 -method BOTH -u domainuser1 -p secretpass
docker run -e PROXY_CONFIG='socks5 127.0.0.1 9050' --network=host ldaprelayscan -dc-ip 10.0.0.20 -method BOTH -u domainuser1 -p secretpass
Error-Based Enumeration Specifics
[LDAPS] Channel Binding Token Requirements
On a Domain Controller that has been patched since CVE-2017-8563, the capability to enforce LDAPS channel binding has existed. The specific policy is called Domain Controller: LDAP server channel binding token requirements and can be set to either Never, When supported, or Always. This is also not required by default (at the time of writing this).
Decrypting and monitoring LDAP over SSL/TLS traffic on a Domain Controller allowed for the identification of a difference in errors during bind attempts when channel binding is enforced versus when it's not. When attempting a bind to LDAP over SSL/TLS using invalid credentials, you will recieve the expected resultCode 49, and in the error message contents you will see data 52e. However, when channel binding is enforced and the LDAP client does not calculate and include the Channel Binding Token (CBT), the resultCode will still be 49, but the error message contents will contain data 80090346 meaning SEC_E_BAD_BINDINGS or that the client's Supplied Support Provider Interface (SSPI) channel bindings were incorrect.

NOTE: Mentions of the
data 8009034error during LDAP over SSL/TLS binding [1] [2] [3] [4] [5]
"Never" vs "When supported" vs "Always"
This specific error makes it easy enough to account for when the Domain Controller: LDAP server channel binding token requirements policy is set to Always. Simply attempt an NTLM-based LDAPS bind using a client that does not support channel binding and look for the data 80090346 within the error in response. But what about when the policy is not set to Always, what about when it's set to When supported? The answer is: bind to LDAPS with NTLM-based authentication and purposefully miscalculate the channel binding information.
First, we need an LDAP client that supports channel binding. SkelSec's implementation of this in msldap will be used to implement a PoC. Channel binding appears as an AV_PAIR value during the NTLM challenge/response process, specifically within the Type 3 or AUTHENTICATE_MESSAGE. Here's another look at some decrypted LDAPS traffic on a Domain Controller to see what a bind attempt from a client supporting channel binding will look like:
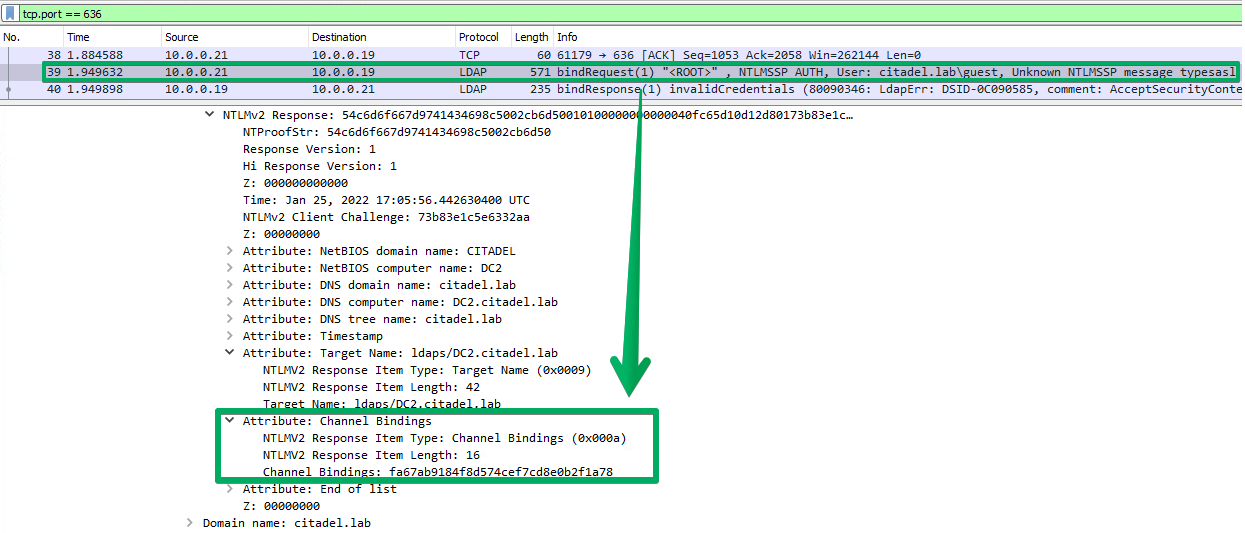
Intentionally miscalculating this value, when the policy in question is set to When supported, will produce the same data 80090346 error. This gives us the ability to differentiate between all possible settings for this policy as it currently exists, from an unauthenticated perspective. How this value is purposefully miscalculated is important, because just manually replacing the value during challenge/response will invalidate the MIC.
[LDAP] Server Signing Requirements
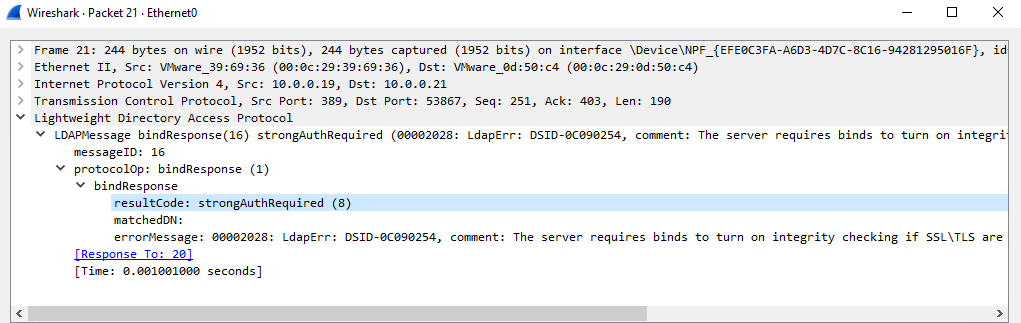
On a Domain Controller, the policy called Domain Controller: LDAP server signing requirements is set to None, Require signing, or it's just not defined. When not defined, it defaults to not requiring signing (at the time of writing this). The error which identifies this protection as required is when a sicily NTLM or simple bind attempt responds with a resultCode of 8, signifying strongerAuthRequired. This will only occur if credentials during the LDAP bind are validated.
References
A few invaluable resources for contextualization of this material and how it fits into common attack scenarios.
- @HackAndDo - NTLM relay
- @_nwodtuhs - NTLM relay mindmap
- @_dirkjan - PrivExchange, the ADCS ESC8 write up, the NTLM relay for RBCD write up, and more
- @domchell - implementation of Farmer and explanation
- @elad_shamir - thorough explanations of abusing RBCD in multiple scenarios, and shadow credentials
- @tifkin_ & @topotam77 - NTLM authentication coercion methods
- @skelsec - msldap w/ support for channel binding