Awesome
δiaphora
<p align='center'> <img src="https://github.com/joxeankoret/diaphora/assets/2945834/3f1e9cf4-98d7-4d9a-b7d3-0a7354053b4e" width="10%"> </p>Diaphora (διαφορά, Greek for 'difference') version 3.1.2 is the most advanced program diffing tool (working as an IDA plugin) available as of today (2024). It was released first during SyScan 2015 and has been actively maintained ever since: Diaphora has been ported to every single minor version of IDA since 6.8 to 8.4.
Diaphora supports versions of IDA >= 7.4 because the code only runs in Python 3.X (Python 3.11 was the last version being tested).
Unique Features
Diaphora has many of the most common program diffing (bindiffing) features you might expect, like:
- Diffing assembler.
- Diffing control flow graphs.
- Porting symbol names and comments.
- Adding manual matches.
- Similarity ratio calculation.
- Batch automation.
- Call graph matching calculation.
- Dozens of heuristics based on graph theory, assembler, bytes, functions' features, etc...
However, Diaphora has also many features that are unique, not available in any other public tool. The following is a non extensive list of unique features:
- Ability to port structs, enums, unions and typedefs.
- Potentially fixed vulnerabilities detection for patch diffing sessions.
- Support for compilation units (finding and diffing compilation units).
- Microcode support.
- Parallel diffing.
- Pseudo-code based heuristics.
- Pseudo-code patches generation.
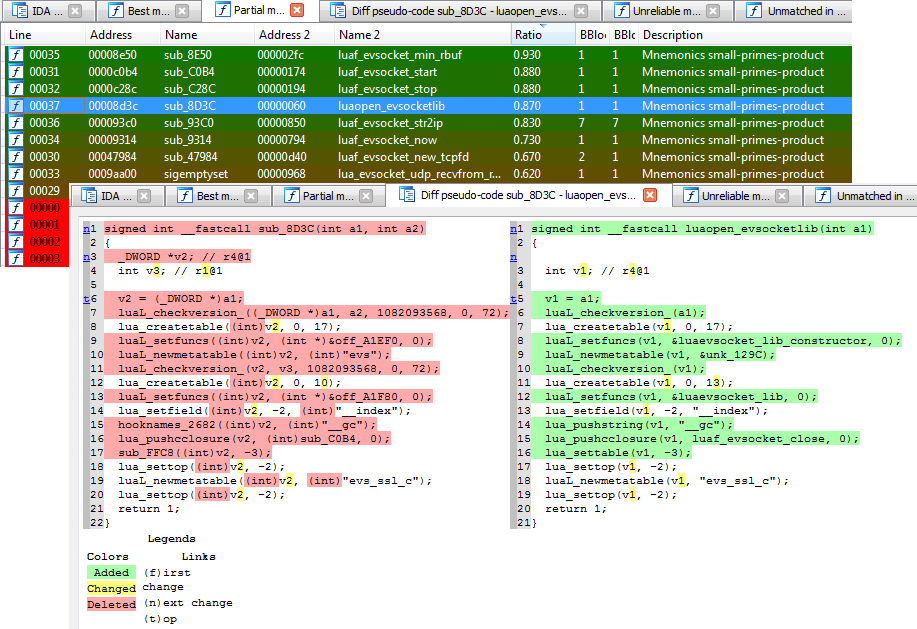
- Diffing pseudo-codes (with syntax highlighting!).
- Scripting support (for both the exporting and diffing processes).
- ...
Installation
Diaphora requires no installation: just download the code and run the script diaphora.py from within IDA or on the command line (only for diffing already exported databases). However, it can be integrated as a plugin into IDA by doing the following:
- Copy
plugins/diaphora_plugin.pyandplugins/diaphora_plugin.cfgto the IDA's plugins directory. - Edit
diaphora_plugin.cfgand set the path value to the Diaphora's directory.
Donations
You can help (or thank) the author of Diaphora by making a donation. If you feel like doing so you can use one of the following links:
Support
Feel free to open issues in Github if you have any problem or need help. If you prefer to chat interactivelly, you can use the following Discord channel: https://discord.gg/atg34w2xjV
Licensing
Versions of Diaphora prior to 1.2.4, including version 1.2.4, were licensed under the GNU GPL version 3. Since version 2.0, Diaphora is now licensed under the GNU Affero GPL version 3 license. The license has been changed so companies wanting to modify and adapt Diaphora cannot offer web services based on these modified versions without contributing back the changes.
For 99.99% of users, the license change doesn't affect them at all. If your company needs a different licensing model, check the next section...
Commercial Support and Consultancy
Commercial support and consultancy is offered for legal companies. If you need support or consultancy for problems you have with your target, to develop products based on Diaphora, to use Diaphora internally interacting with your own tools, for plagiarism detection projects, etc... you can contact me at admin@joxeankoret.com for more details.
Licensing problems
If your company does not allow using the AGPL license, you can get commercial licenses of Diaphora to use it in your company, or to use it as a particular in any company you work (similar concept as IDA's named licenses). For more details, please contact me at admin@joxeankoret.com.
Wiki
If you are looking to how to automate the export or diffing process, or you want to speed operations, etc... You might want to take a look to the wiki where such questions are answered.
Screenshots
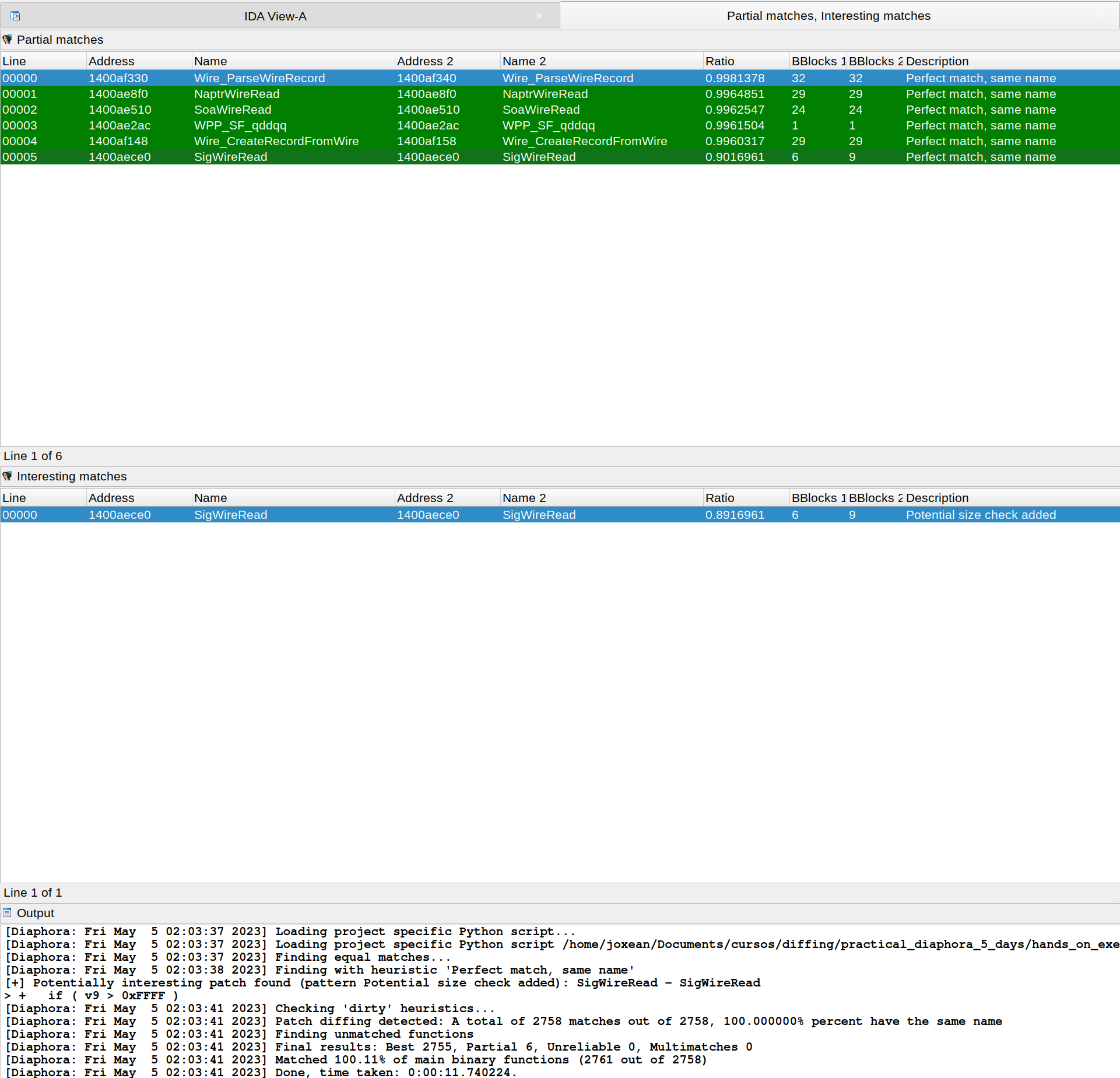
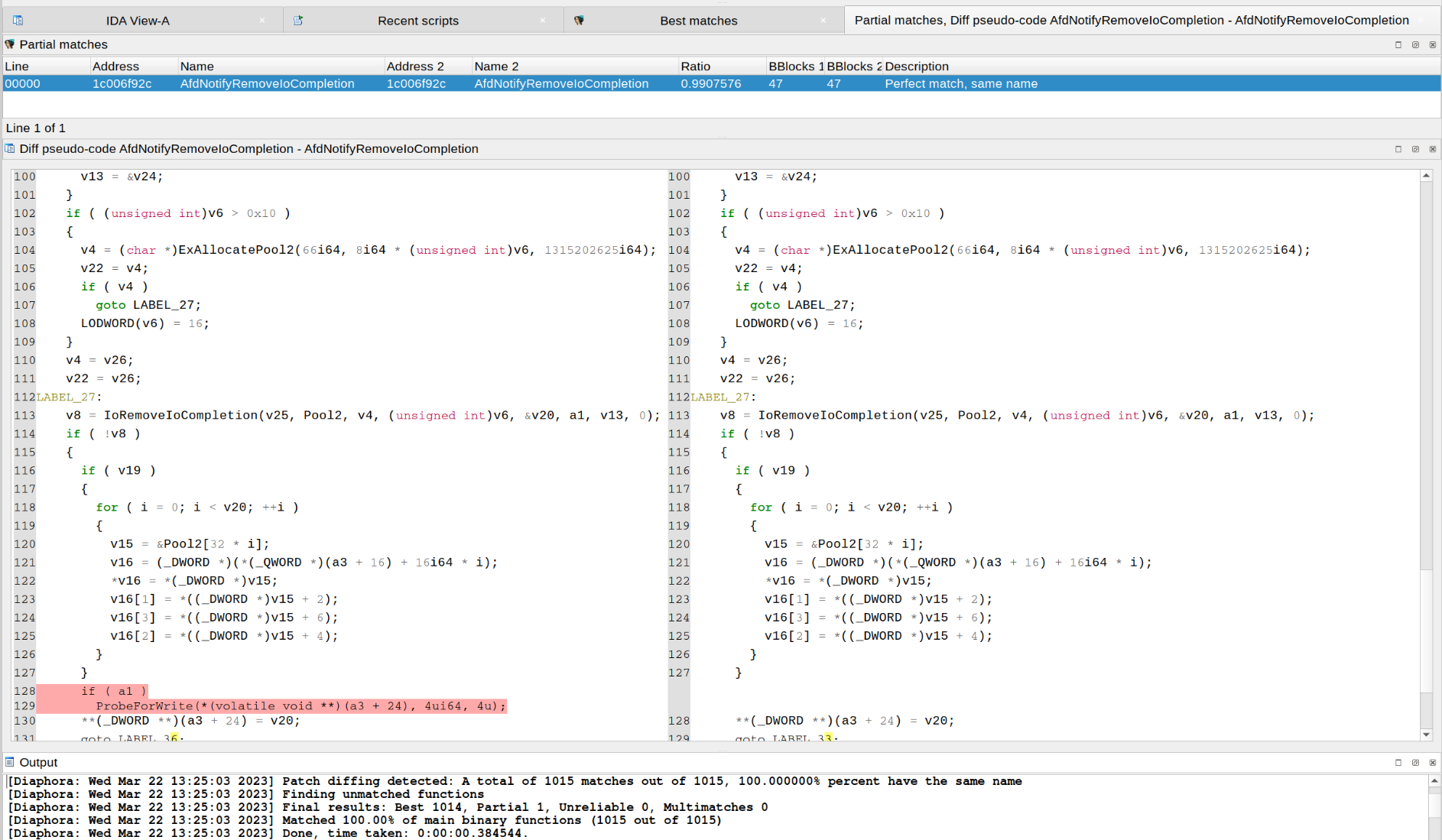
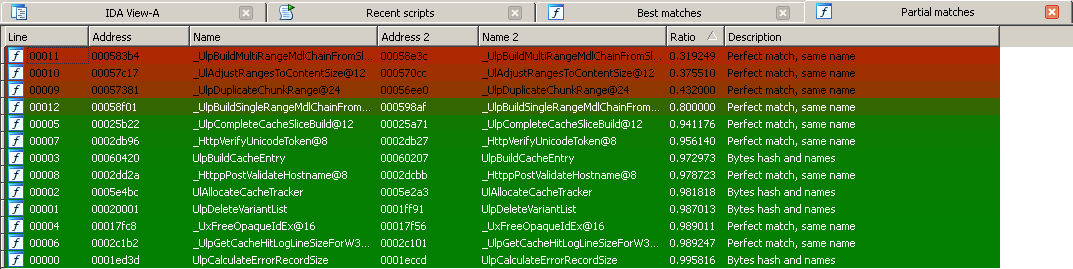
Diaphora finding the exact function where a vulnerability was patched in CVE-2020-1350:
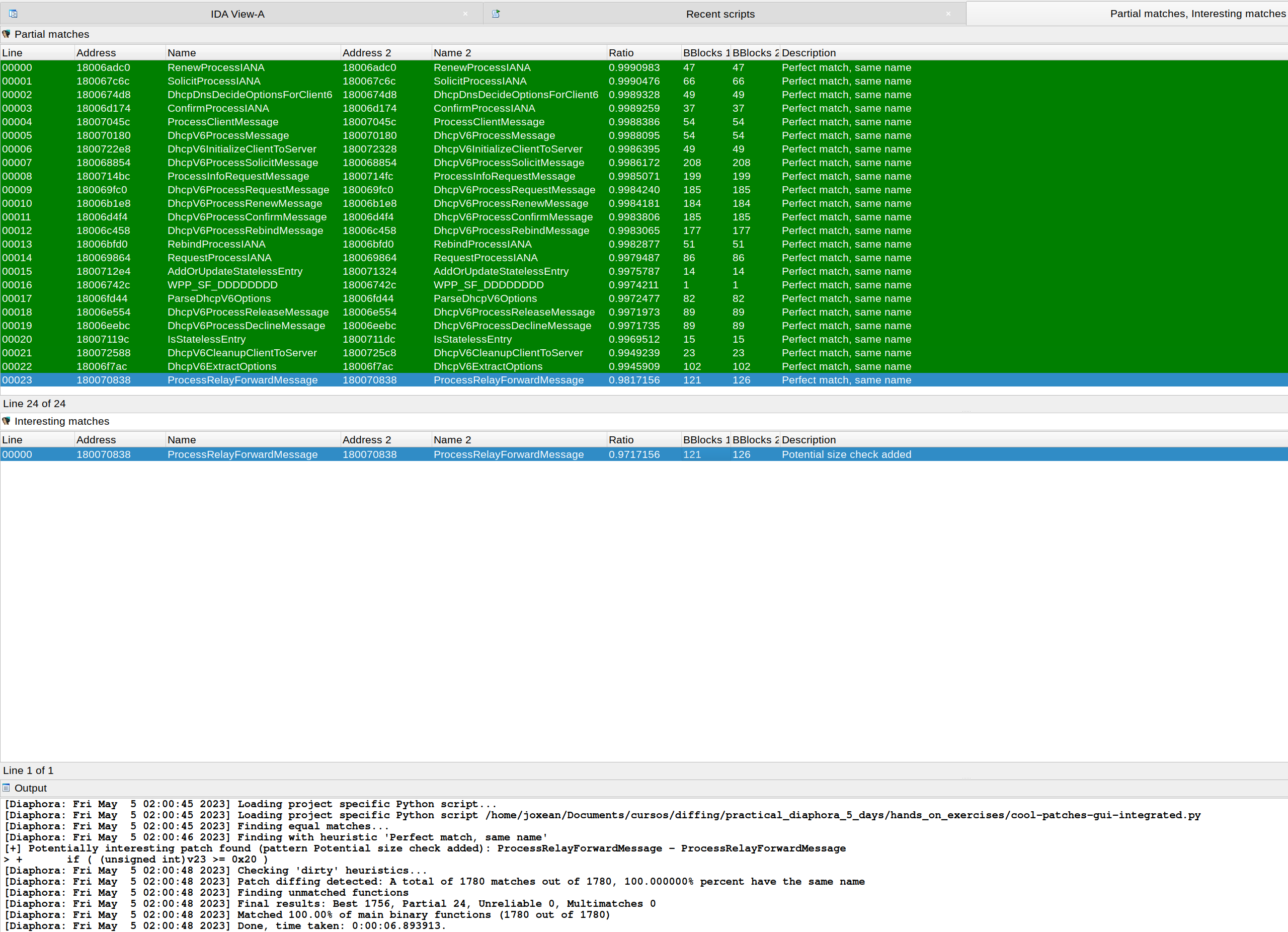
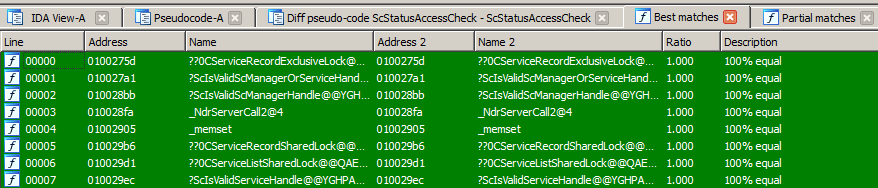
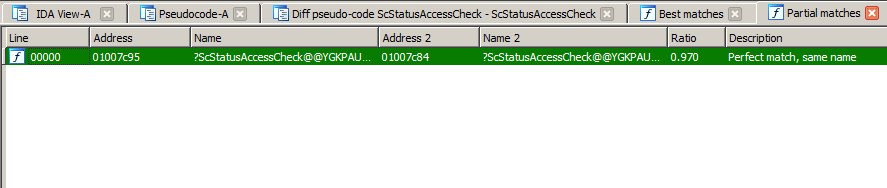
Diaphora, again, finding the exact function where CVE-2023-28231 was fixed:
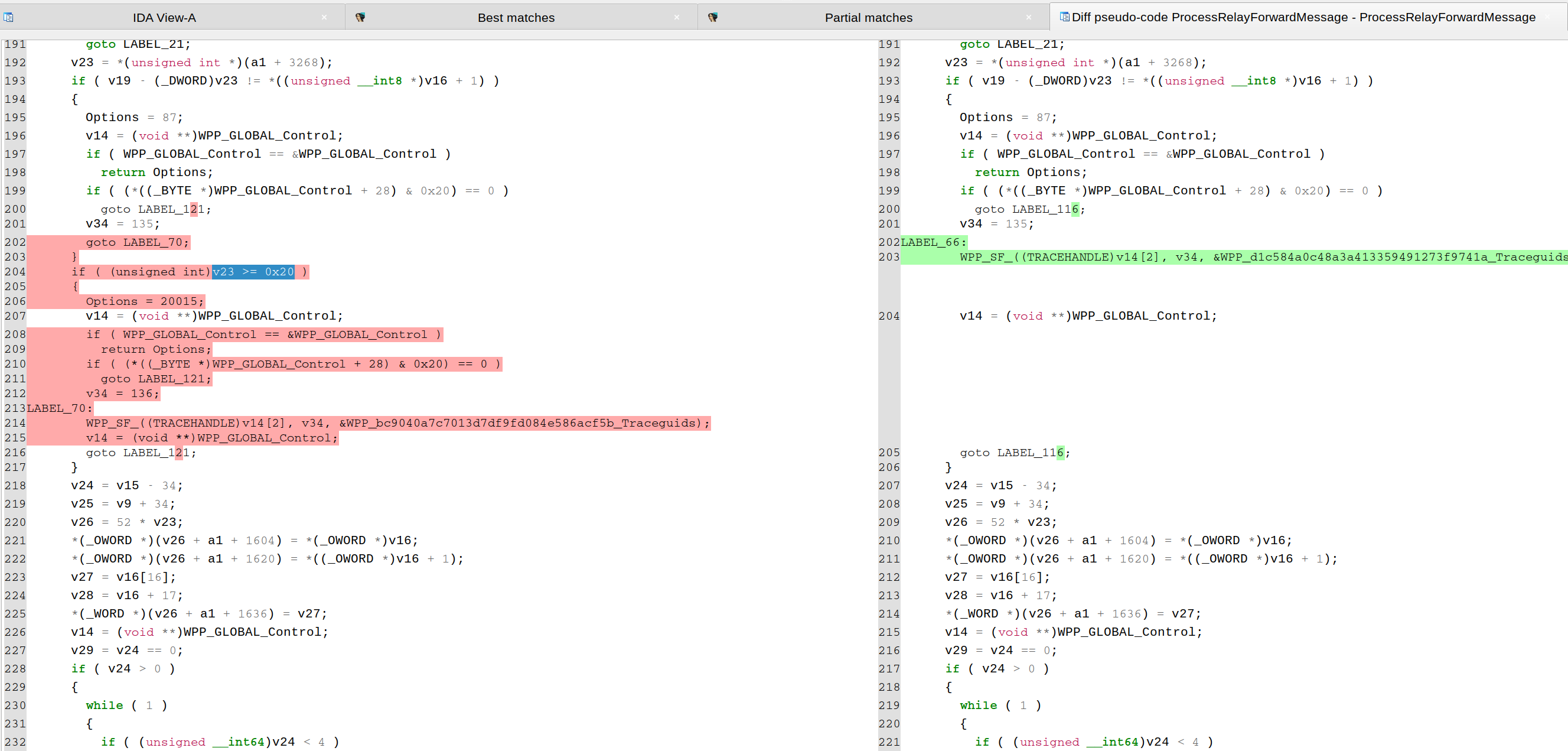
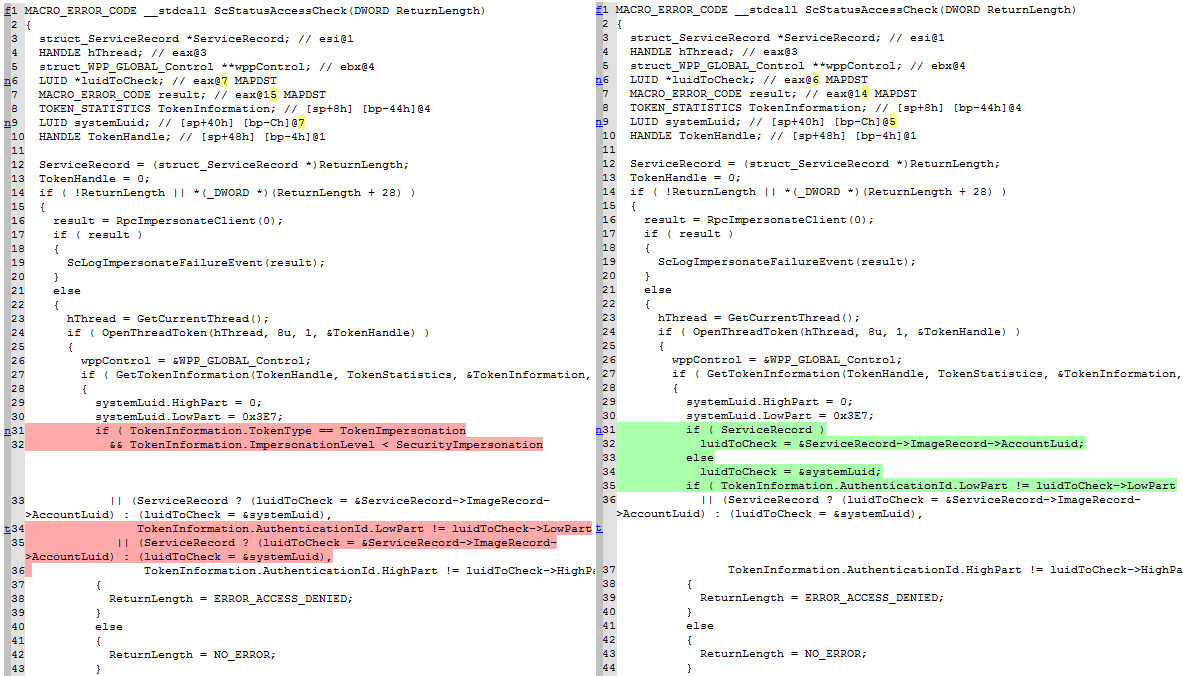
CVE-2023-28231. As explained in a blog from ZDI, the vulnerability was fixed by checking that the number of relay forward messages in "ProcessRelayForwardMessage()" is not bigger or equal than 32 (0x20), as shown in the following pseudo-code diffing:
Diaphora doing Hex-Ray's microcode diffing:
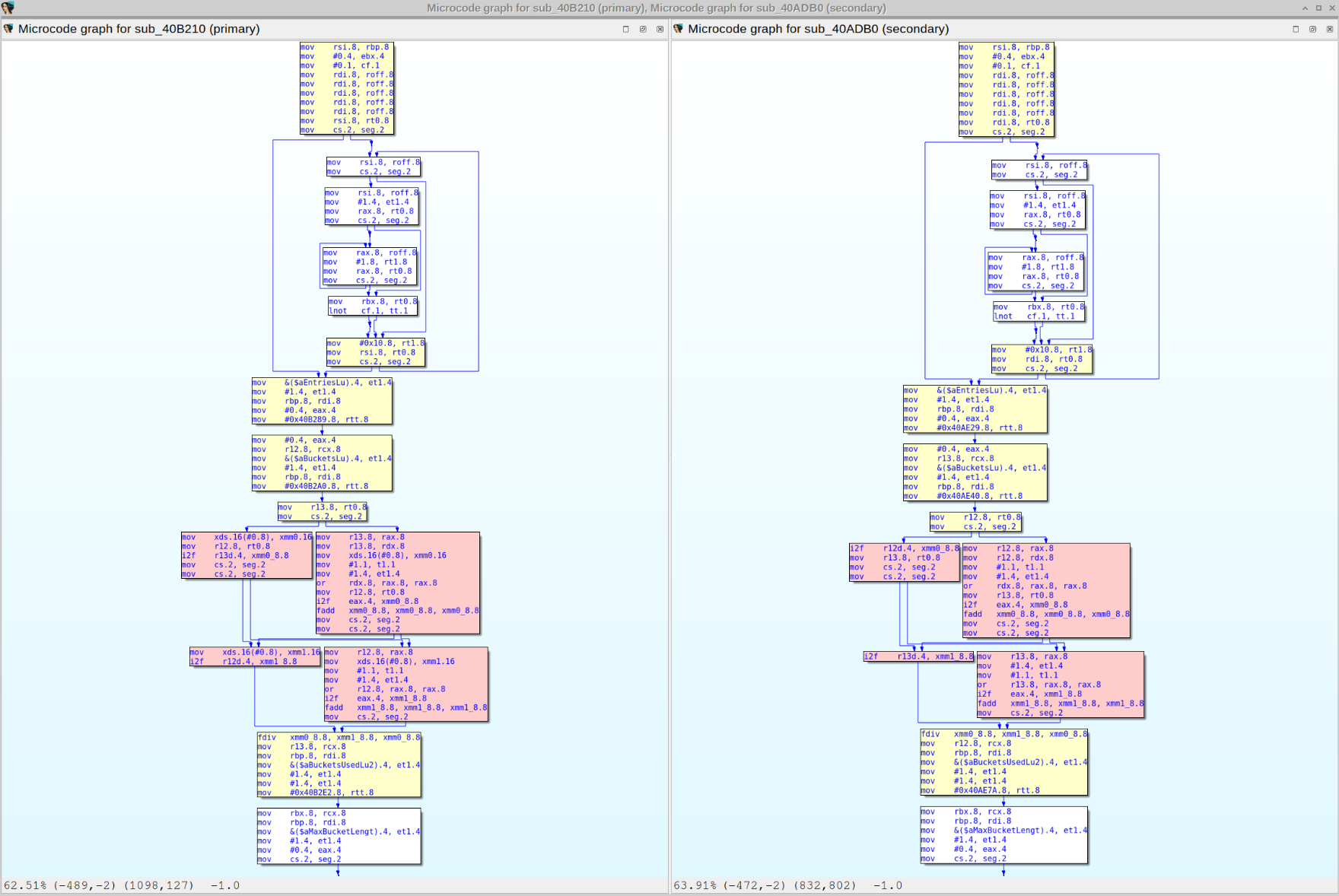
Diffing assembly, pseudo-code and microcode:
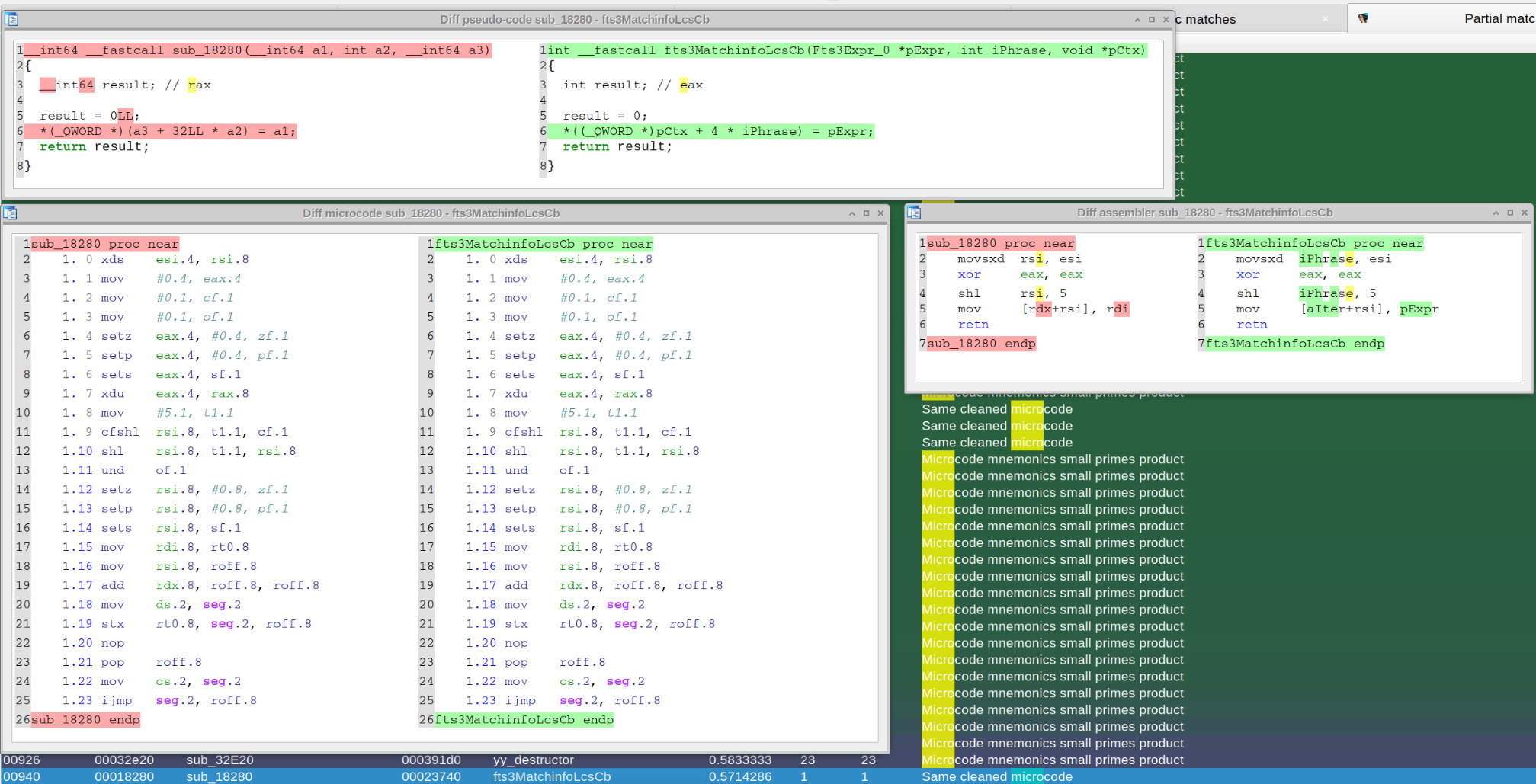
Diffing CVE-2023-21768 with Diaphora 3.0:
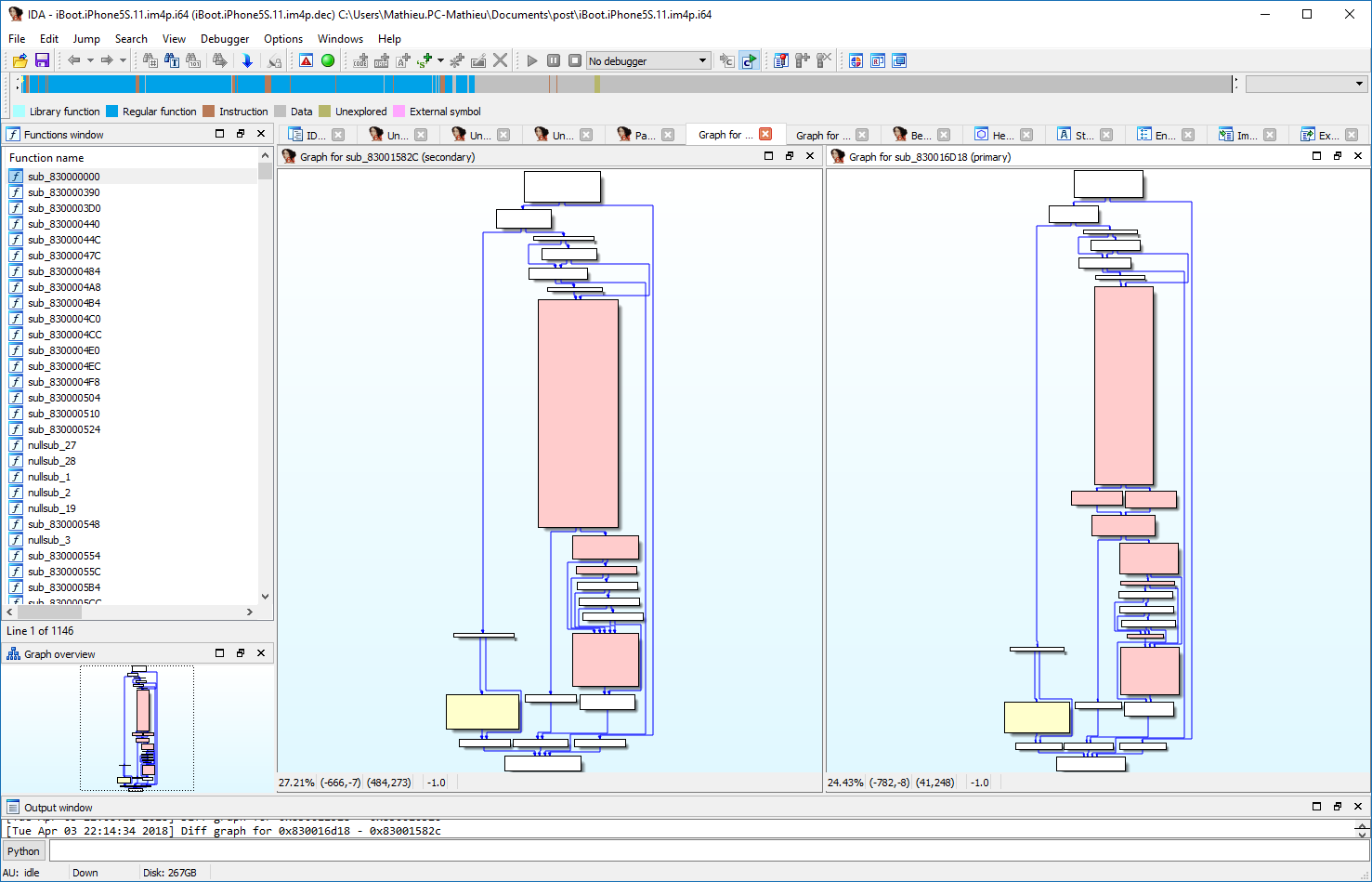
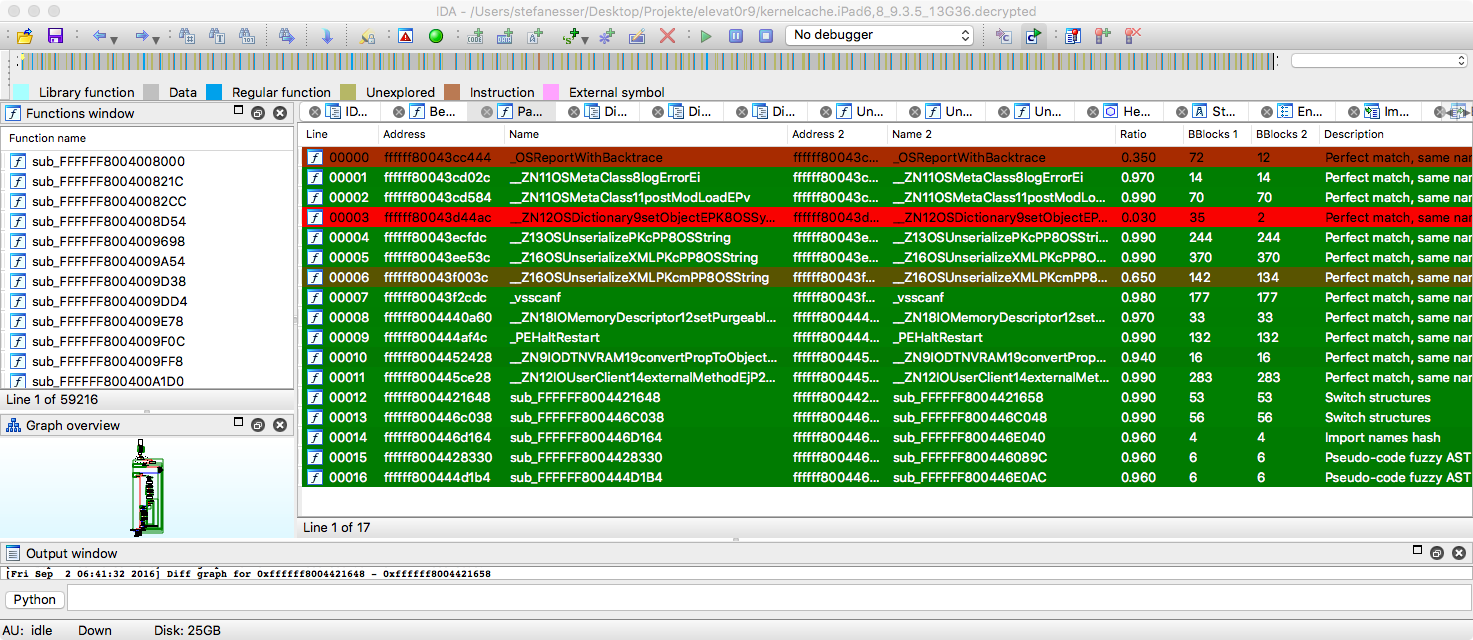
This is a screenshot of Diaphora diffing the PEGASUS iOS kernel Vulnerability fixed in iOS 9.3.5:
And this is an old screenshot of Diaphora diffing the Microsoft bulletin MS15-034:
These are some screenshots of Diaphora diffing the Microsoft bulletin MS15-050, extracted from the blog post Analyzing MS15-050 With Diaphora from Alex Ionescu.
Here is a screenshot of Diaphora diffing iBoot from iOS 10.3.3 against iOS 11.0: