Awesome
DInvoke_shellcodeload_CSharp
Blog link: May not gonna update.
-
A ShellcodeLoader base on my another project(https://github.com/Kara-4search/Simple_ShellCodeLoader_CSharp), inspire by TheWover(https://github.com/TheWover).
-
The purpose is to bypass EDR 's APIs hook, or danger APIs dectection.
-
Use D/Invoke to load shellcode into memory.
-
I removed a lot of unnecessary code from the original project, make the code easy for understanding.
-
You could change the function name or do other magic works make it better for EDR bypassing.
-
I only tested it on x86 with the shellcode below(It is a calc shellcode), but it should be able to work on x64.
byte[] codepent = new byte[193] { 0xfc,0xe8,0x82,0x00,0x00,0x00,0x60,0x89,0xe5,0x31,0xc0,0x64,0x8b,0x50,0x30, 0x8b,0x52,0x0c,0x8b,0x52,0x14,0x8b,0x72,0x28,0x0f,0xb7,0x4a,0x26,0x31,0xff, 0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0xc1,0xcf,0x0d,0x01,0xc7,0xe2,0xf2,0x52, 0x57,0x8b,0x52,0x10,0x8b,0x4a,0x3c,0x8b,0x4c,0x11,0x78,0xe3,0x48,0x01,0xd1, 0x51,0x8b,0x59,0x20,0x01,0xd3,0x8b,0x49,0x18,0xe3,0x3a,0x49,0x8b,0x34,0x8b, 0x01,0xd6,0x31,0xff,0xac,0xc1,0xcf,0x0d,0x01,0xc7,0x38,0xe0,0x75,0xf6,0x03, 0x7d,0xf8,0x3b,0x7d,0x24,0x75,0xe4,0x58,0x8b,0x58,0x24,0x01,0xd3,0x66,0x8b, 0x0c,0x4b,0x8b,0x58,0x1c,0x01,0xd3,0x8b,0x04,0x8b,0x01,0xd0,0x89,0x44,0x24, 0x24,0x5b,0x5b,0x61,0x59,0x5a,0x51,0xff,0xe0,0x5f,0x5f,0x5a,0x8b,0x12,0xeb, 0x8d,0x5d,0x6a,0x01,0x8d,0x85,0xb2,0x00,0x00,0x00,0x50,0x68,0x31,0x8b,0x6f, 0x87,0xff,0xd5,0xbb,0xf0,0xb5,0xa2,0x56,0x68,0xa6,0x95,0xbd,0x9d,0xff,0xd5, 0x3c,0x06,0x7c,0x0a,0x80,0xfb,0xe0,0x75,0x05,0xbb,0x47,0x13,0x72,0x6f,0x6a, 0x00,0x53,0xff,0xd5,0x63,0x61,0x6c,0x63,0x2e,0x65,0x78,0x65,0x00 }; -
You could use API monitor(http://www.rohitab.com/apimonitor) to test the project, comparing with the SimpleLoader(https://github.com/Kara-4search/Simple_ShellCodeLoader_CSharp), You could see there is no API call via D/Invoke.
-
Kernel functions are not good enough,you could even do the ntdll version of this.
Usage
- Just replace the shellcode.
- Launch it through some white list applications
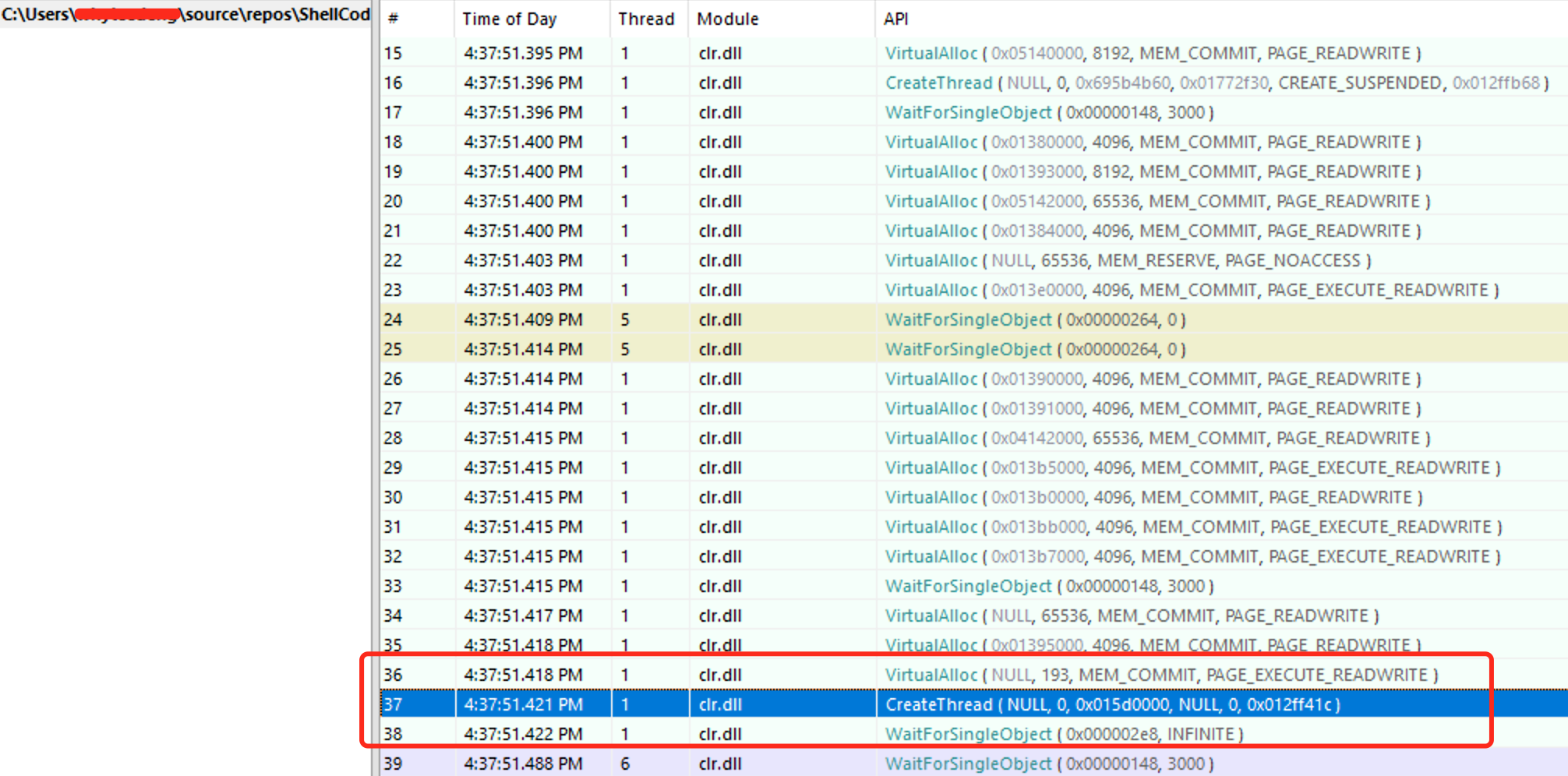
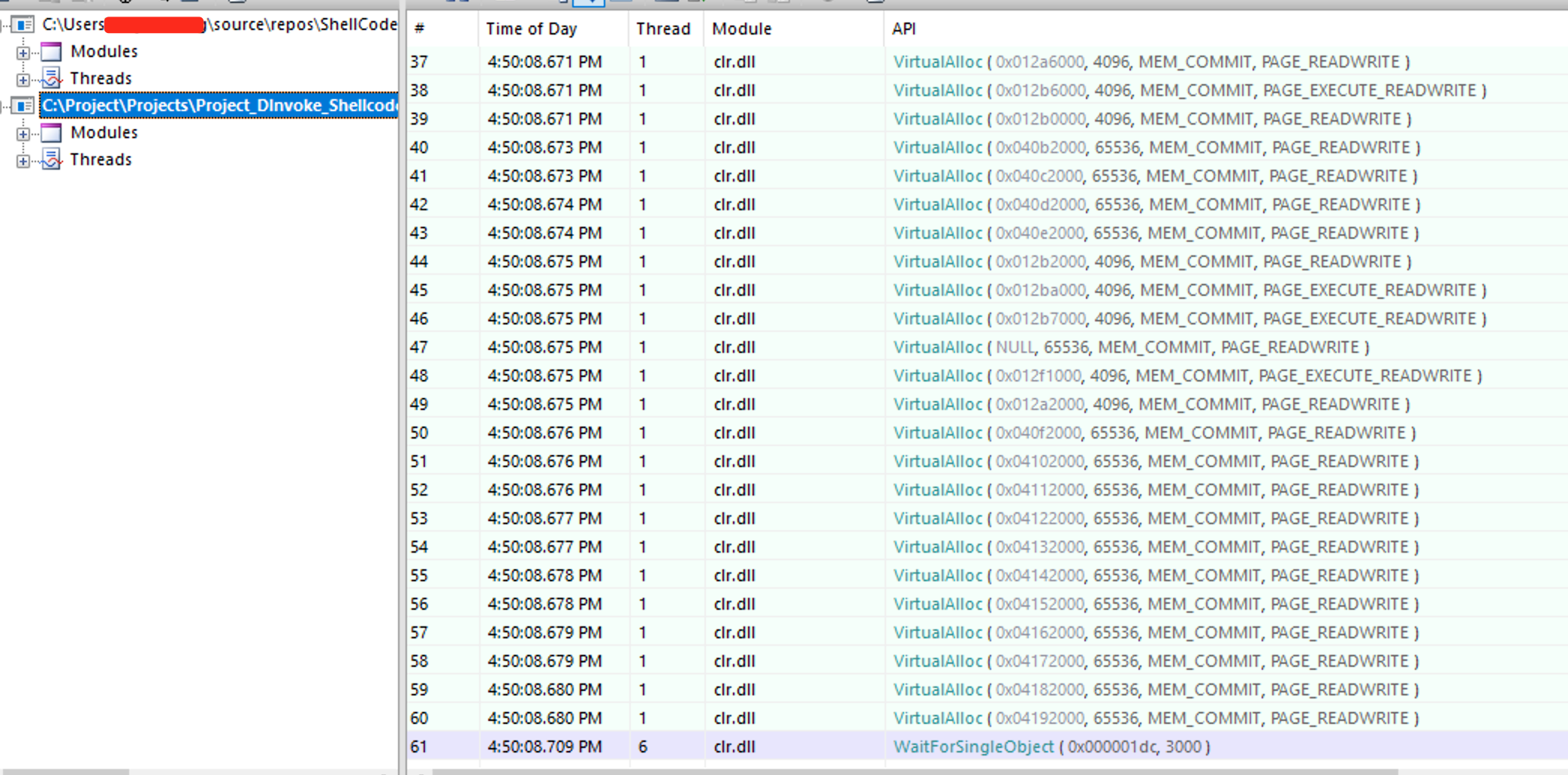
Comparing via API monitor
There are mainly 3 APIs we are gonna monitor:
-
VirtualAlloc
-
CreateThread
-
WaitForSingleObject
-
You could see the picture below, the SimpleLoader' s API call caught by API monitor.
-
And the DInvoke ShellcodeLoader's API call was not caught by API monitor.
Reference link:
- https://github.com/CCob/SharpBlock
- https://ethicalchaos.dev/2020/05/27/lets-create-an-edr-and-bypass-it-part-1/
- https://ethicalchaos.dev/2020/06/14/lets-create-an-edr-and-bypass-it-part-2/
- https://thewover.github.io/Dynamic-Invoke/
- https://offensivedefence.co.uk/posts/dinvoke-syscalls/
- https://github.com/TheWover/DInvoke
- http://www.rohitab.com/discuss/topic/38807-api-monitor-v2-r10-release-instant-monitoring-without-definitions-support-for-dllmain-and-early-apis-windows-8/
- https://vimeo.com/566964438
- https://docs.microsoft.com/en-us/windows/win32/api/processthreadsapi/nf-processthreadsapi-createthread
- https://docs.microsoft.com/en-us/dotnet/api/microsoft.visualstudio.shell.interop.vsdebugstartupinfo.dwcreationflags?view=visualstudiosdk-2019